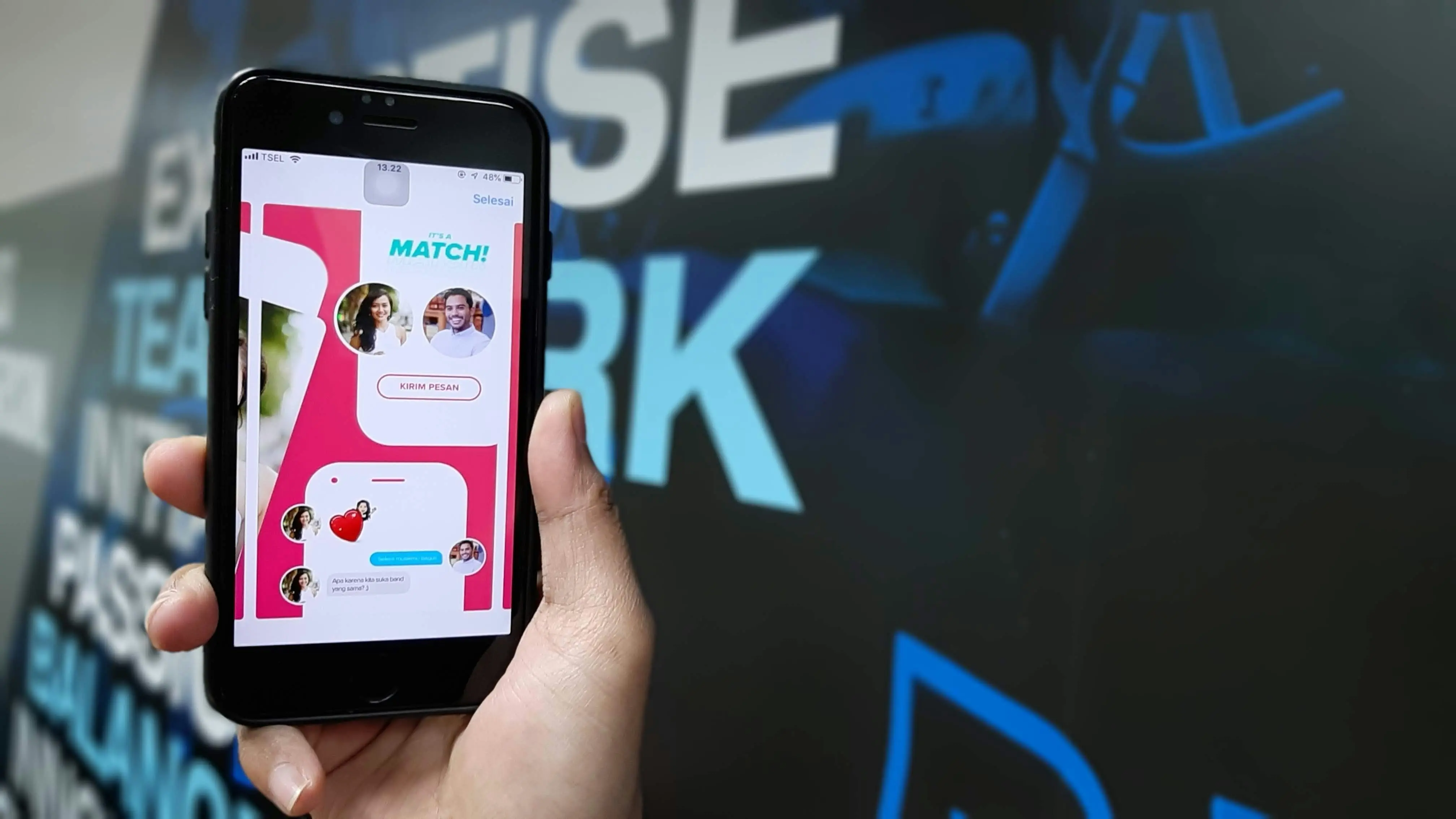
Online dating has made meeting new people easier than ever—but it has also created new privacy risks. If you’re using Tinder, your photos are your first impression. Unfortunately, they can also be copied, misused, or weaponized by impersonators.
Why Image Theft Happens on Tinder
Tinder is one of the most widely used dating platforms in the world. With millions of users swiping daily, it’s also an attractive hunting ground for scammers and impersonators.
Common reasons your images might be stolen:
- Catfishing scams – Someone pretends to be you.
- Romance scams – Your photos are used to lure victims. Fake profiles are frequently used in romance scams, where scammers build trust with victims before attempting to steal money or sensitive details, including financial information.
- Fake social media accounts – Your identity is cloned.
- Harassment or revenge tactics
- Bot accounts – Automated profiles using stolen photos.
The more attractive, professional, or distinctive your photos are, the more likely they may be targeted. Scammers may also target your financial information and attempt to steal money through these scams.
1. Be Strategic About the Photos You Upload
Not all photos carry the same level of risk.
Avoid:
- High-resolution professional portraits
- Images with identifiable home addresses
- Photos showing license plates
- Work badges or uniforms with logos
- Photos also used on public social media profiles
Consider:
- Slightly lower resolution images
- Photos not used anywhere else online
- Cropped versions of full-resolution originals
Pro Tip: If your Tinder photos are identical to your public Instagram or LinkedIn images, they’re easier to reverse-search.
2. Turn Off “Smart Photos” (Optional but Strategic)
Tinder’s Smart Photos feature automatically tests and reorders your pictures. While convenient, it may increase visibility and engagement—meaning your photos get seen (and potentially screenshotted) more often. Regularly running a reverse image search on your photos can help you determine if they're being used elsewhere without your permission.
If privacy is your priority, manually control which photos appear and in what order.
3. Use Reverse Image Search to Monitor Misuse
Regularly check whether your photos appear elsewhere online:
- Google Reverse Image Search
- TinEye
- Yandex Image Search
If your image shows up on suspicious profiles, act immediately.
4. Add Subtle Deterrents
While watermarks aren’t attractive on dating profiles, subtle strategies can discourage theft:
- Slightly obscure background details
- Use photos taken specifically for dating apps
- Avoid overly polished influencer-style shots
Scammers prefer clean, versatile images they can reuse anywhere.
5. Strengthen Your Tinder Account Security
Beyond images, account security matters.
Enable:
- Phone number verification
- Two-factor authentication (if available)
- Verified profile badge
Tinder’s verification system (blue checkmark) adds legitimacy to your real account and makes it easier for others to spot imposters.
6. What To Do If Someone Steals Your Photos
If you discover impersonation:
Step 1: Report the Fake Profile
Use Tinder’s in-app reporting system immediately. Users can report suspicious activity to the app's support team to enhance their safety, and these reports are important for investigation and verification of fake profiles or impersonators.
Step 2: Document Everything
- Take screenshots
- Save URLs
- Record dates and usernames
Step 3: File a Report with Tinder
Submit a formal complaint through Tinder’s support page.
Step 4: Submit a DMCA Takedown (If Necessary)
If your photos appear on websites or social platforms, you can request removal under copyright law.
7. Watch for Signs You’re Being Cloned
Red flags include:
- Friends asking why you matched with them
- Messages from strangers referencing conversations you never had
- Duplicate profiles using your name
- Accounts using your exact bio
If multiple signs appear, investigate quickly.
8. Extra Privacy Practices for Online Dating
To reduce broader exposure:
- Use a Google Voice number instead of your primary phone
- Avoid sharing personal social media immediately
- Delay giving out your last name
- Meet in public places
- Tell a friend before meeting someone
Privacy isn’t paranoia—it’s digital self-defense.
9. Understand the Bigger Picture: Romance Scam Ecosystems
Stolen Tinder photos often end up in global romance scam networks. Criminal groups reuse images repeatedly across platforms. Your face could be part of dozens of fake profiles without you knowing.
Tinder collects a wide range of personal information, including phone numbers, email addresses, and location data. Scammers may also obtain your images or data from other sources, such as social media or partner websites, increasing the risk of impersonation.
Victims of these scams sometimes believe they are in long-term relationships with impersonators. Reporting misuse doesn’t just protect you—it protects potential victims.
10. Should You Use Tinder at All?
Millions use Tinder safely every day. The platform itself isn’t the enemy—poor privacy habits are.
By:
- Limiting personal data
- Monitoring your images
- Acting quickly on misuse
- Staying security-aware
You dramatically reduce your risk.
Quick Overview And Goals
- define impersonation risk for dating apps
- state guide objectives and target readers
Why Stolen Photos Happen On Dating Apps
- explain how stolen photos enable fake profiles
- list common photo-sourcing channels used by impersonators
- note consequences for victims’ reputation and safety
Secure Your Social Media Accounts To Prevent Stolen Photos
- enable two-factor authentication on social media accounts
- set all profile photos and posts to private
- remove publicly tagged images you don’t control
How To Use Reverse Image Search To Verify A Profile
- save suspect profile photos for searching
- run photo through multiple reverse image search engines
- interpret matches and trace original social media accounts
- document search results with screenshots and URLs
Identifying Fake Profiles And Red Flags On Online Dating
- spot inconsistent bios and vague personal details
- watch for rushed emotional appeals or financial requests
- check for multiple profiles using similar photos
- verify account activity and message patterns
Step-By-Step: Remove Stolen Photos From A Fake Tinder Profile
- gather proof copies of stolen photos from social media
- take timestamps and screenshots of the fake profile
- submit an impersonation report to Tinder using the form
- follow up with supporting documents via Tinder support email
Reporting Outside Tinder: Escalation And Legal Options
- report the impersonator profile to the host platform
- file a DMCA takedown with image-hosting sites if applicable
- consult local law enforcement for identity-theft complaints
Use Face Check And Video Selfie Features For Verification
New users on Tinder are required to take a short video selfie as part of the Face Check feature to verify their identity. This process helps ensure that profiles are genuine and prevents impersonation or fake accounts. The Face Check system has been shown to reduce exposure to potential bad actors by more than 60% in regions where it is deployed. Once a user successfully completes Face Check, they receive a 'Photo Verified' badge on their profile, which should be kept visible to enhance trust. The video selfie taken for Face Check is deleted after verification, but the encrypted FaceMap and FaceVector are retained for account authenticity checks.
We recommend enabling video selfie verification when available to further protect your images and identity on Tinder.
Preventive Photo Practices For Dating App Profiles
- replace public photos with non-identifying images
- watermark sensitive images before posting publicly
- remove metadata from photos before uploading
Recovery And Follow-Up After Impersonation
- change passwords across affected accounts immediately
- review account privacy settings and connected apps
- notify friends and contacts about the impersonation
Reporting Checklist And Communication Templates
- create a concise impersonation report template
- prepare a checklist of documents to attach
- log all correspondence and removal confirmations
Encryption and Data Protection
When it comes to online dating, protecting your personal details and profile photos is more important than ever. Tinder, like many leading dating apps, has invested heavily in encryption and data protection to help users guard against identity theft, fake profiles, and romance scams.
Tinder’s parent company, Match Group, uses advanced encryption to secure all user data—including messages, uploaded photos, and video selfies. This means that even if a scammer creates a fake account using stolen photos, your sensitive information remains protected from unauthorized access. Encryption ensures that your personal information, from profile photos to chat messages, is only accessible to you and those you choose to connect with.
To further boost security and authenticity, Tinder offers a verification badge for users who complete the Face Check process. This feature uses biometric data to confirm that you are the same person shown in your profile photos, making it much harder for scammers to create convincing fake accounts. The blue verification badge is a visible sign to other Tinder users that your profile is genuine, helping everyone identify real people and avoid potential romance scams.
Tinder also empowers users with privacy tools and features that put you in control of your information. You can decide which photos and videos to upload, limit who can see your content, and adjust your privacy settings to suit your comfort level. These options help reduce the risk of your images being misused or your identity being compromised.
All of these measures are backed by Tinder’s commitment to following applicable law and upholding strict community guidelines. The platform’s policies are designed to prevent harassment, hate speech, and other harmful behaviors, creating a safer environment for everyone. If you ever encounter a fake profile or suspect your photos have been stolen, Tinder’s reporting tools and support team are there to help you take swift action.
By understanding and using Tinder’s security features—like encryption, Face Check, and privacy controls—you can better protect yourself from identity theft, financial loss, and other risks associated with online dating. Whether you’re new to dating apps or a seasoned user, staying informed and proactive is the best way to keep your online interactions safe and secure.
Final Thoughts
Your Tinder photos represent your identity. In the wrong hands, they can become tools for deception.
Think of your dating profile like your digital front door:
- Control what’s visible
- Lock down what matters
- Monitor for misuse
Online dating should feel exciting—not stressful. With the right precautions, you can swipe confidently while keeping your identity protected.
FAQs
1. Can someone really steal my photos from Tinder?
Yes. While Tinder does not provide a direct “download” button for images, anyone can take screenshots. Scammers frequently copy photos to create fake profiles, run romance scams, or impersonate users on other platforms.
2. How can I check if someone is using my pictures?
Use reverse image search tools like Google Images or TinEye. Upload one of your Tinder photos and see where else it appears online. If you find suspicious profiles, document everything and report it immediately.
3. What should I do if I find a fake profile using my photos?
Take screenshots of the impersonating account, including usernames and URLs. Then:
- Report the profile directly within Tinder
- Submit a complaint through Tinder’s support page
- Request removal from any external websites hosting the fake account
If necessary, you can also submit a DMCA takedown request to have your copyrighted images removed.
4. Does Tinder offer protection against impersonation?
Tinder provides profile verification (blue checkmark), reporting tools, and moderation systems to detect suspicious activity. While these measures help, no platform can completely prevent screenshots or off-platform misuse. Users should combine platform tools with personal privacy practices.
5. How can I reduce the risk of my photos being stolen in the first place?
To lower your risk:
- Avoid using the same photos across multiple public platforms
- Skip high-resolution professional images
- Don’t include identifiable personal details (home address, workplace badge, etc.)
- Regularly monitor your photos with reverse image search
Being selective and proactive significantly reduces your chances of impersonation.